>> Continued From the Previous Page <<
Through a FOIA request, Yehuda Miller just obtained the 2020 Election Infrastructure (EI) Subsector Cyber Risk Summary study.
Based on non-attributable cybersecurity patterns that were seen between November 3, 2019, and November 3, 2020—Election Year 2020 (EY20)—the paper offers analysis, conclusions, and suggestions.
The data for Election Year 2020 that CISA officials were aware of was included in the report, which was released in March 2021.
CISA’s 2020 examination of the US Election Infrastructure (EI) organizations was released on page two of the report.
Following a review of the data available for evaluated EI entities, CISA discovered:
** 76% of EI entities for which CISA performed a Risk and Vulnerability Assessment (RVA) had spearphishing weaknesses, which provide an entry point for adversaries to launch attacks
** 48% of entities had a critical or high severity vulnerability on at least one internet accessible host providing potential attack vectors to adversaries
** 39% of entities ran at least one risky service on an internet-accessible host, providing the
opportunity for threat actors to attack otherwise legitimate services** 34% of entities ran unsupported operating systems (OSs) on at least one internet accessible host, which exposes entities to compromise.
The following are our own highlights from page two of the report:
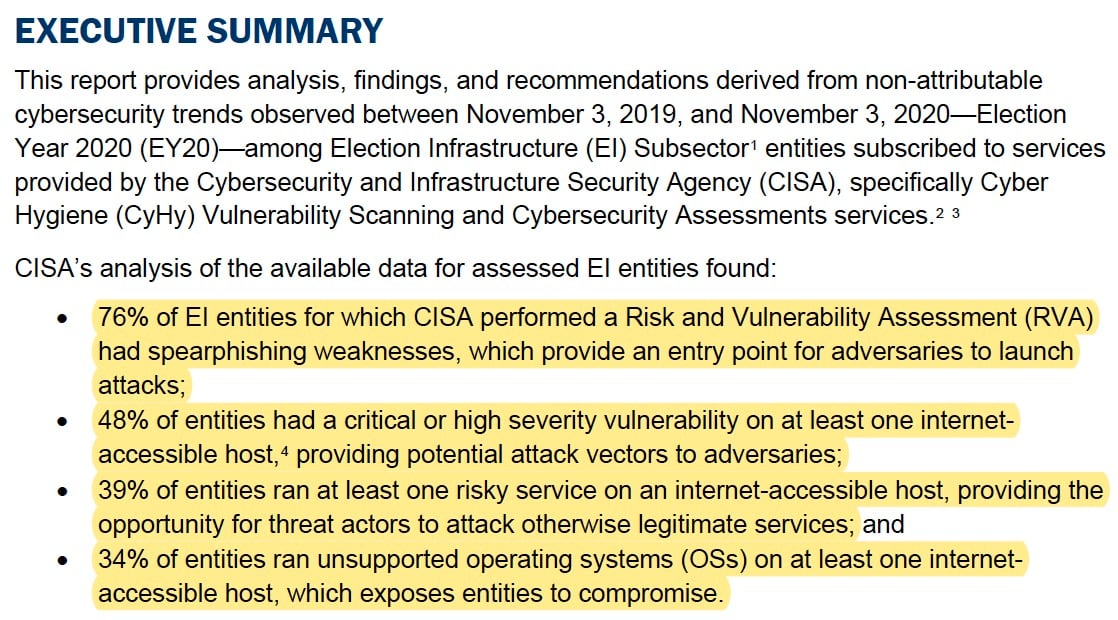
Given that 48% of the organizations had a critical or high vulnerability on at least one host that was accessible via the internet, and 76% of the electoral infrastructure had spearfishing vulnerabilities, how can 2020 be deemed a “secure” election?
The CISA study then goes on to explain how election officials may fix these systemic flaws. This obviously implies that foreign entities can still exploit the flaws.
The report’s page four details how an Advanced Persistent Threat (APT) was able to collect voter registration information in the United States!
An APT actor initiated an election-related misinformation operation in the run-up to the 2020 election after successfully obtaining voter registration information in the United States, including in at least one case from a state election website. CISA also noted in October 2020 that APTs were targeting the networks of state, local, tribal, and territorial (SLTT) government bodies with regard to electoral infrastructure. CISA does not have any evidence as of October 24, 2020, to suggest that the integrity of electoral data had been compromised.
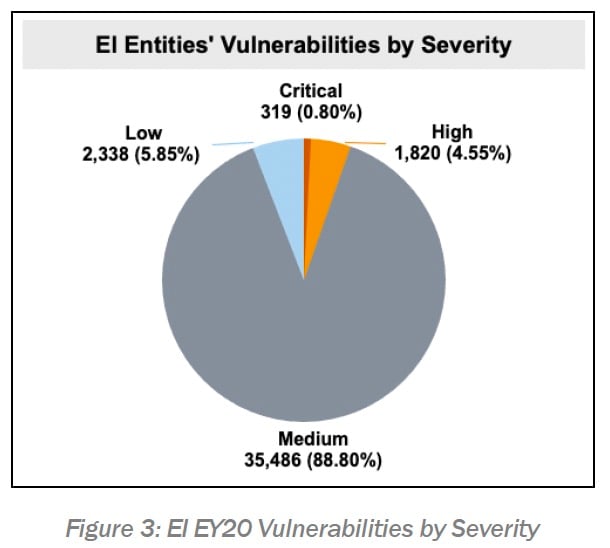
The report’s seventh page details how CISA CyHy scanning found 48,796 vulnerabilities in total on hosts across the 324 participating EI companies.
Based on the CVSS base score, 319 (0.80%) of the vulnerabilities were of critical severity, while 1,820 (4.55%) were of high severity.
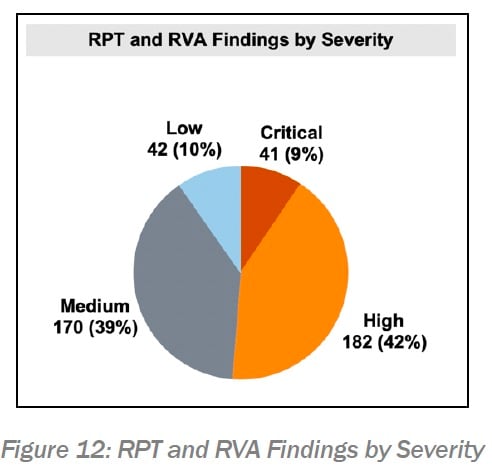
Authorities discovered an additional 451 flaws and vulnerabilities in the systems, according to page fifteen of the study.
CISA completed RVAs and RPTs for 108 EI firms in EY20. Penetration testing, phishing assessments, web application assessments, and database examinations were carried out by RPT and RVA teams. These teams found 451 discoveries, or flaws and vulnerabilities that pose a risk to the entity (see figure 12).
Do you think that sounds safe?
How can anyone argue that the 2020 election was “the most secure election ever” when, according to his agency’s own reporting, 39% of the infrastructure ran at least one risky service on an internet-accessible host, 48% of the infrastructure had critical or high severity vulnerabilities, and 76% of the infrastructure had spearphishing weaknesses?
Further information on spearphishing attacks is covered on pages fifteen and sixteen of the report.
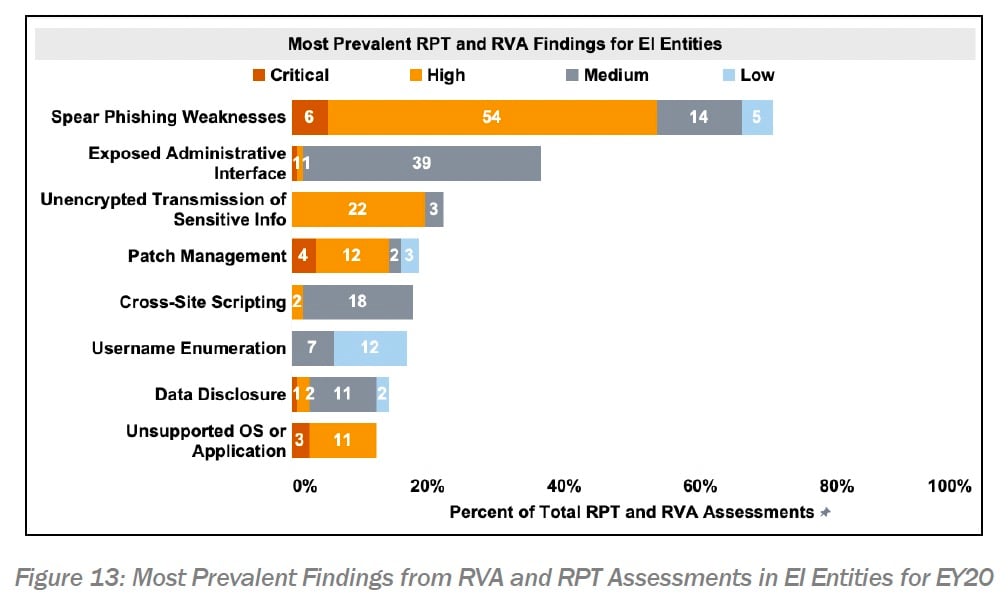
The most frequent finding found in 73 percent of the businesses throughout the examinations was spearphishing flaws (see figure 13). The widespread effectiveness of spearphishing suggests that the entities under assessment have insufficient security at the host and border levels. With the help of a user action, such as clicking a link or opening a file that starts the execution of malicious payloads, this vulnerability allowed spearphishing emails to cross the network border and then execute on the local host. Apart from suggesting an inadequate or nonexistent deployment of technology safeguards, this discovery may also signify a deficiency in cybersecurity knowledge and the inability of people to identify spearphishing attempts, so rendering the organization susceptible. All EI entities should study and take action on this discovery, as many threat actors frequently launch attacks by using spearphishing to get credentials and gain first remote access.
Chris Krebs, a former employee of the DHS, and his ridiculous testimony made before the US Senate under oath are thoroughly discredited by this CISA study.
It seems clear that Krebs lied to the Senate Committee in 2020.
In the coming days, Yehuda Miller and The Gateway Pundit want to release other damaging papers.





